CompTIA SecurityX
Master everything you need to know in order to pass the CompTIA SecurityX certification exam.
PURCHASE NOW

Course Introduction
In today’s enterprise environments, cybersecurity requires more than foundational knowledge—it demands advanced technical expertise, strategic decision-making, and the ability to architect secure solutions at scale. This course prepares you for the CompTIA SecurityX certification exam, validating your ability to design, implement, and manage complex security solutions in real-world environments.
You’ll begin with Security Architecture, where you’ll design resilient enterprise security solutions across hybrid, cloud, and on-premises infrastructures. This includes applying Zero Trust principles, secure DevOps practices, cryptographic implementations, and advanced identity and access management strategies to protect large-scale systems.
Next, in Security Engineering and Implementation, you’ll focus on integrating advanced security controls into complex environments. You’ll work with virtualization, containerization, cloud-native technologies, automation, and orchestration, ensuring secure configuration and deployment across enterprise systems.
The Security Operations and Incident Response module emphasizes hands-on defensive techniques, threat hunting, monitoring, digital forensics concepts, and advanced incident response strategies. You’ll learn how to assess and respond to sophisticated threats while maintaining operational resilience and business continuity.
In Governance, Risk, and Compliance, you’ll evaluate enterprise risk, apply regulatory frameworks, and align security initiatives with business objectives. This section prepares you to translate technical risk into executive-level communication and to support organizational security strategy.
By the end of this course, you’ll be equipped to architect, engineer, and defend enterprise environments against evolving threats—demonstrating the advanced skills required to confidently earn your CompTIA SecurityX certification and operate as a senior-level security practitioner.
What you'll learn
Enterprise Security Architecture
Design secure, scalable enterprise environments using Zero Trust principles, segmentation strategies, and resilient system architecture across hybrid and cloud infrastructures.
Advanced Threat, Vulnerability & Risk Analysis
Assess advanced threats and vulnerabilities using qualitative and quantitative risk analysis to recommend enterprise-level security mitigations.
Security Engineering & Technology Integration
Implement and integrate advanced security controls across cloud, virtualized, and DevSecOps-driven enterprise environments.
Security Operations & Incident Response
Conduct enterprise-level monitoring, threat hunting, and incident response to strengthen resilience and operational continuity.
Governance, Risk & Compliance Strategy
Align security strategy with business objectives through governance frameworks, risk evaluation, and regulatory compliance oversight.
Enterprise Cryptography & Identity Management
Architect secure cryptographic systems and identity controls to protect high-value enterprise assets.
Course Pricing

6 MONTH ACCESS
WHATS INCLUDED
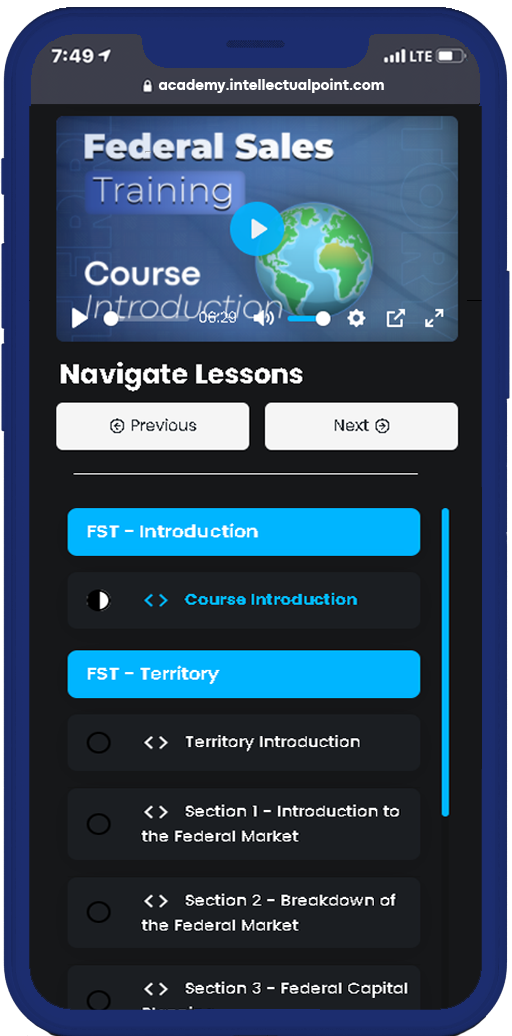
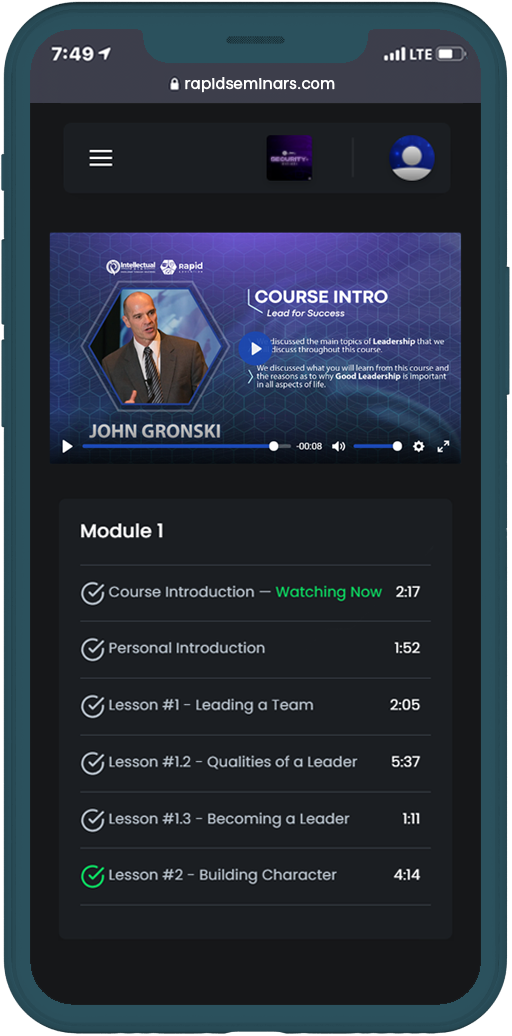
Course Curriculum
Example Curriculum
- Apply Software Development (15:07)
- Integrate Software Architecture (15:12)
- Support Operational Resilience (16:31)
- Implement Cloud Infrastructure (26:33)
- Integrate Zero Trust Concepts (14:59)
- Troubleshoot Using AAA and IAM (24:19)
- Dynamic Application Security Testing (DAST) (37:41)
- Evaluating Attack Surface Management and Reduction (37:54)
- Designing a CI/CD Pipeline (25:22)
- Evaluating Information and Data Security Design (15:30)
- Configuring Intrusion Detection Systems (IDS) (36:55)
- Testing a Web Application Firewall (WAF) (18:03)
- Investigating and Remediating Vulnerabilities (23:24)
- Detecting Shadow IT (18:28)
- Implementing API Security (20:09)
- Securing Kubernetes Deployments in Azure (21:11)
- Implementing Continuous Authentication (34:27)
- Enhance Endpoint Security (20:41)
- Configure Network Infrastructure (21:33)
- Initiate Security Automation (14:55)
- Apply Cryptography Concepts (25:04)
- Configuring HIPS/HIDS (Host-Based Intrusion Protection System/Host-Based Detection System) (28:51)
- Implementing Host-Based Firewalls (29:57)
- Troubleshooting Network Misconfigurations (27:21)
- Implementing Event-Based Triggers (19:05)
- Apply Security Orchestration, Automate, and Response (SOAR) Framework (23:06)
- Perform Threat Modeling (12:26)
- Examine Security Monitoring (11:35)
- Analyze Known Attack Methods and Associated Mitigations (20:25)
- Apply Threat Hunting Tools and Technologies (12:06)
- Evaluate Incident Analysis and Response (11:22)
- Implementing MITRE ATT@CK Framework (11:22)
- Establishing Behavior Baselines and Analytics (31:28)
- Logging Auditing and Alerting (14:36)
- Investigating External Intelligence Sources (26:06)
- Investigating Indicators of Compromise (IoC) (34:30)
- Auditing Indicators of Attack (15:39)
- Conducting Malware Analysis (22:29)
- Extracting and Analyzing Metadata (23:14)
Start Your Learning
Journey Today
Learn how to design, configure, and secure networks using the core principles of networking.